How to generate public and private keys for SSH on Mac OS X 10.8 Mountain Lion and then share that public key on another device and have it so that no password is prompted for a secure connection to a remote computer.
First thing that you need to do on your OSX machine is to create a directory that will store your SSH keys. Then you will generate a public and private key for your account, launch the Terminal and punch in some commands:
Create the Keys
Get into your Home
cd
Create a SSH directory name .ssh and move into it
mkdir .ssh ; cd .ssh
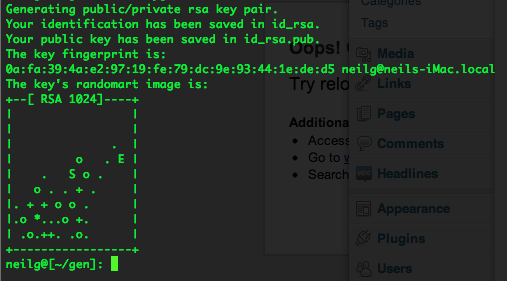
Creates your private and public key, the blank quotes at the end of the command gives the private key no password, so allowing for automatic logins!
ssh-keygen -b 1024 -t rsa -f id_rsa -P ""
Change into and list the contents of your .ssh directory
cd .ssh ; ls -la
-rw------- 1 username staff 887B Jun 1 11:35 id_rsa <--Your private key--> -rw-r--r-- 1 username staff 239B Jun 1 11:35 id_rsa.pub <--Your public key-->
Thats your SSH keys created, don’t give out the private one always keep that one only on your local machine.
Share the Keys
Create an authorized_keys file if you want remote machines to connect to you – you then can add in remote public keys.
touch authorized_keys
You can create automatic logins by adding the contents of your public key to a corresponding remote device in the authorized_keys file in the remote home user directory on the remote device ”.ssh“.
To see and copy your public key:
Displays your public SSH key, which you can copy and add to another remote computer
cat id_rsa.pub
ssh-rsa AAAAB3NzaC1yc2EAAAABIwAAAIEA2CtcmYRmQJX04pZnrTPrU68BZMk9YlbI6CUcFUp RVw29p V7mxW16wd/q9z7n+xytqdp4wsAc/7+24ZVikMhhRetEGr3LSBz5gm9980oTPEy61+pDP2y jafShe5xcszIUnQ rN1ohCuF7Y/a/TG6G6gaJGcLexUiwfTRtCAbpuzfU= [email protected]
On the remote computer if needed, change the permssions on the authorized_keys file to write to add the public key, on a new line paste in your public key, and change permissions back to read only after for security:
chmod a-w authorized_keys
Paste the entire id_rsa.pub content with vi or nano into the authorized_keys file, if using nano use the -w flag to not use weird line breaks.
If the remote host does not have an “authorized_keys” file simply create one and after the public key is pasted in don’t forget to takeaway write permissions.
Going Both Ways
So now when you connect via SSH no password is prompted as the remote computer has your public key which is in turn only decrypted by your private key held in your local .ssh/ directory. If you want the communications to be bilateral then repeat the process in the opposite order between the two.
Now the two computers can securely connect with no password prompting, making it ideal to script between the two for file copies or back ups.
Doing it Quicker
Now instead of typing in
ssh [email protected]
Make an alias in your bash shell you could alias it to
alias now='ssh [email protected]'
Then all you have to type in is
now